Cyber Warfare: US 2026 Threat Report on State-Sponsored Attacks

The U.S. government’s 2026 threat assessment details a significant surge in state-sponsored cyberattacks, emphasizing the critical need for enhanced national cybersecurity defenses against sophisticated global adversaries.
The digital battlefield is constantly expanding, and understanding its evolving landscape is paramount for national security. The recent release of the Cyber Warfare: U.S. Government Releases 2026 Threat Assessment Report on State-Sponsored Attacks offers a stark look into the sophisticated challenges facing the United States, highlighting the urgent need for robust defensive strategies.
The Escalating Threat Landscape of State-Sponsored Cyberattacks
The 2026 Threat Assessment Report paints a concerning picture of an increasingly aggressive and capable array of state-sponsored actors. These entities, backed by national governments, are not merely seeking data; they aim to disrupt critical infrastructure, influence political processes, and gain strategic advantages through persistent, often covert, digital campaigns. This section delves into the report’s key findings regarding the scale and sophistication of these threats.
The nature of cyber warfare has shifted significantly, moving beyond simple data breaches to encompass complex, multi-vector attacks designed for maximum impact. Adversaries are investing heavily in advanced persistent threats (APTs), which can remain undetected within networks for extended periods, gathering intelligence and preparing for decisive strikes. The report emphasizes that no sector is truly immune, from defense contractors to public utilities.
Advanced Persistent Threats (APTs) and Their Impact
APTs are characterized by their stealth, persistence, and focus on high-value targets. Unlike opportunistic cybercriminals, state-sponsored APT groups possess significant resources, highly skilled personnel, and long-term objectives aligned with national interests. Their operations often involve extensive reconnaissance, custom malware development, and sophisticated evasion techniques to bypass conventional security measures.
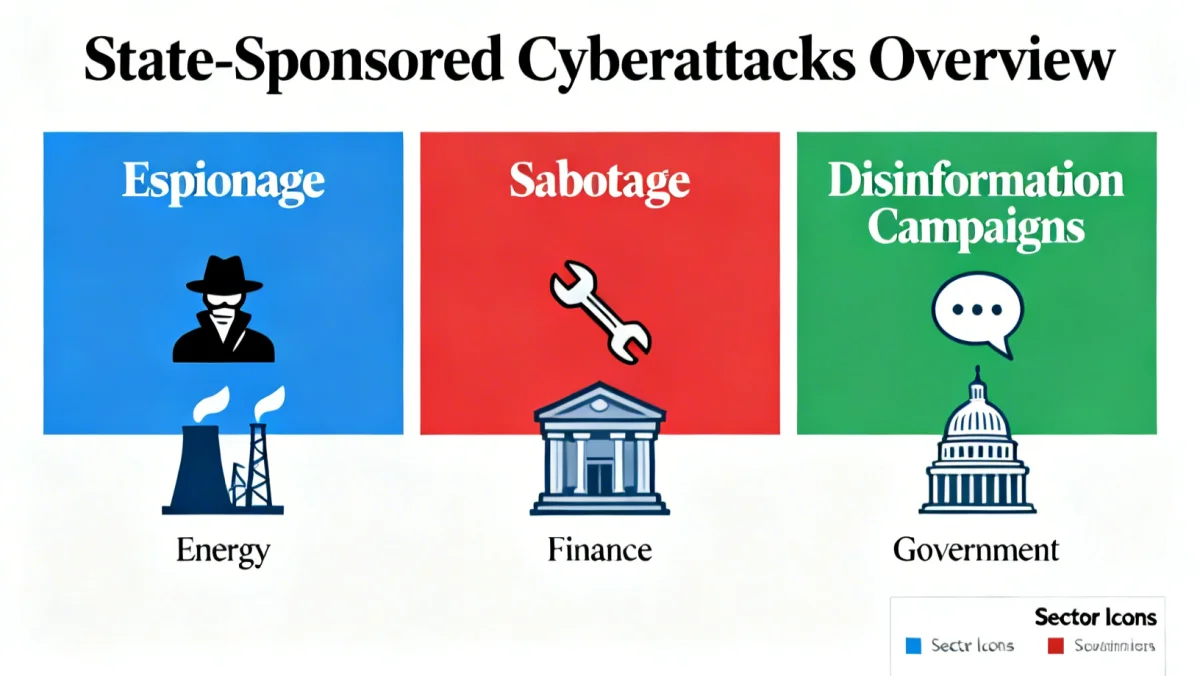
- Espionage: Stealing sensitive government, corporate, and research data for economic and strategic gain.
- Sabotage: Disrupting critical infrastructure, such as power grids, transportation systems, and financial networks, to create chaos or gain leverage.
- Disinformation: Manipulating public opinion and political discourse through social media and compromised news outlets to sow discord and undermine trust.
- Intellectual Property Theft: Illegally acquiring trade secrets and technological blueprints to accelerate national industrial and military development.
The report concludes that the sheer volume and increasing complexity of these APTs represent a fundamental shift in the global security paradigm. Understanding their methodologies and motivations is the first step toward developing effective countermeasures.
Key Adversaries and Their Cyber Capabilities
The 2026 report specifically identifies several nations as primary actors in state-sponsored cyber warfare, each possessing unique capabilities and strategic objectives. While the report refrains from naming specific countries to maintain diplomatic channels, it provides detailed profiles of the types of threats posed by these entities, allowing for targeted defense strategies. These adversaries leverage a combination of human intelligence and technological prowess to achieve their goals.
One prominent adversary, often described as a major global power, is noted for its extensive use of cyber espionage to gain economic and military advantages. Their campaigns are characterized by a focus on intellectual property theft and long-term infiltration of critical supply chains. Another nation, recognized for its aggressive and disruptive tactics, frequently employs cyberattacks to project power and destabilize regions, often targeting democratic processes and essential services.
Evolving Tactics of State-Sponsored Actors
Adversarial tactics are constantly evolving, adapting to new defenses and exploiting emerging technologies. The report highlights a growing reliance on zero-day exploits, supply chain compromises, and the weaponization of artificial intelligence (AI) for automated attack generation and enhanced targeting. These methods make detection and attribution increasingly difficult, demanding a proactive and adaptive defense posture.
- Zero-Day Exploits: Leveraging previously unknown software vulnerabilities to gain unauthorized access before patches are available.
- Supply Chain Attacks: Compromising software or hardware vendors to inject malicious code into products used by target organizations.
- AI-Powered Attacks: Using artificial intelligence to automate reconnaissance, tailor phishing campaigns, and accelerate malware development, making attacks more efficient and effective.
- Hybrid Warfare Integration: Combining cyber operations with traditional military, economic, and political pressure to achieve strategic objectives.
The assessment underscores that these adversaries are not static; they continuously refine their tools and techniques, necessitating a dynamic and intelligence-driven response from the U.S. government and its partners. Staying ahead requires constant vigilance and investment in cutting-edge cybersecurity research.
Impact on U.S. Critical Infrastructure and National Security
The core concern of the 2026 Threat Assessment Report is the direct and indirect impact of state-sponsored cyberattacks on the U.S. critical infrastructure and overall national security. These attacks are not theoretical; they represent tangible threats to the nation’s economic stability, public safety, and governmental functions. The report details several scenarios and actual incidents where such infrastructure has been targeted.
Critical infrastructure, encompassing sectors like energy, water, transportation, healthcare, and financial services, forms the backbone of modern society. A successful, widespread cyberattack on any of these sectors could lead to catastrophic consequences, including widespread power outages, disruptions in essential services, financial market instability, and even loss of life. The interconnected nature of these systems means a breach in one area can quickly cascade across others.
Real-World Implications and Potential Disasters
The report outlines how even seemingly minor intrusions can have significant long-term effects. For instance, prolonged data exfiltration from research institutions can undermine technological advancement, while tampering with electoral systems can erode public trust in democratic processes. The economic costs associated with responding to and recovering from these attacks are also substantial, diverting resources from other vital areas.
- Energy Grid Disruption: Cyberattacks on power grids could cause widespread blackouts, impacting millions and paralyzing economic activity.
- Financial System Instability: Breaches in financial institutions can lead to market manipulation, data theft, and a loss of confidence in the banking sector.
- Healthcare System Compromise: Attacks on hospitals and healthcare providers can disrupt patient care, compromise sensitive medical records, and have life-threatening consequences.
- Water Treatment Facility Tampering: Malicious actors could gain control of water treatment systems, potentially compromising public health.
Ultimately, the report stresses that protecting critical infrastructure is not just a technical challenge but a national imperative. It requires a multi-faceted approach involving government agencies, private sector partners, and international allies to create resilient defenses.
U.S. Government’s Defensive Strategies and Initiatives
In response to the escalating threats outlined in the 2026 assessment, the U.S. government has significantly bolstered its defensive strategies and launched new initiatives. These efforts are designed to create a more resilient national cybersecurity posture, capable of deterring, detecting, and responding to sophisticated state-sponsored attacks. The approach is comprehensive, involving technological advancements, policy changes, and enhanced collaboration.
One key strategy involves strengthening the Cybersecurity and Infrastructure Security Agency (CISA) and other federal bodies dedicated to cybersecurity. Their mandates have been expanded to include more proactive threat hunting, real-time intelligence sharing with the private sector, and the implementation of advanced defensive tools across government networks. The focus is on moving from a reactive stance to a predictive and preventative one.
Technological Advancements and Policy Enhancements
The report highlights several critical areas of investment and development. These include the deployment of next-generation intrusion detection systems, the adoption of zero-trust architectures across federal agencies, and significant funding for quantum-resistant cryptography research. Policy-wise, new regulations are being considered to mandate higher cybersecurity standards for critical infrastructure operators, ensuring a baseline level of protection across vulnerable sectors.
- Zero-Trust Architecture: Implementing security models that require strict verification for every user and device attempting to access network resources, regardless of their location.
- Quantum-Resistant Cryptography: Investing in and developing encryption methods that can withstand attacks from future quantum computers, protecting long-term data integrity.
- Enhanced Threat Intelligence Sharing: Streamlining the process of sharing real-time threat data between government agencies, private companies, and international partners to facilitate rapid response.
- Cyber Resilience Programs: Developing programs that focus not only on preventing attacks but also on quickly recovering and maintaining essential functions if a breach occurs.
These initiatives reflect a recognition that cybersecurity is a continuous battle, requiring ongoing adaptation and innovation. The government is committed to leveraging the best available technology and expertise to safeguard national interests.
The Role of International Cooperation in Cyber Defense
Cyber warfare transcends national borders, making international cooperation an indispensable component of any effective defense strategy. The 2026 Threat Assessment Report underscores the critical importance of alliances and partnerships in combating state-sponsored cyberattacks. No single nation can unilaterally address the global nature of these threats; collective action is essential for shared security and resilience.
The United States is actively engaging with its allies, including NATO members and key partners in the Indo-Pacific region, to develop joint cyber defense protocols, share threat intelligence, and coordinate responses to major incidents. These collaborations aim to create a unified front against malicious actors, presenting a stronger deterrent and a more robust collective defense. Information sharing agreements and joint exercises are becoming more frequent and sophisticated.
Building Global Cyber Resilience
International cooperation extends beyond military alliances to encompass diplomatic efforts and capacity building. The U.S. is working with developing nations to enhance their cybersecurity capabilities, recognizing that weaker links in the global digital chain can be exploited by adversaries. Promoting international norms of responsible state behavior in cyberspace is also a key diplomatic objective, aiming to establish clear red lines and reduce the likelihood of conflict.
- Joint Cyber Exercises: Conducting simulated cyberattack scenarios with allies to test response protocols and improve interoperability.
- Intelligence Sharing Agreements: Formalizing channels for rapid and secure exchange of threat intelligence with trusted international partners.
- Capacity Building: Providing training and resources to allied nations to strengthen their cybersecurity infrastructure and expertise.
- Norms Development: Advocating for international agreements and principles that govern state conduct in cyberspace, promoting peace and stability.
These collaborative efforts are vital for creating a more secure global digital environment, ensuring that the collective defense is stronger than any individual adversary’s offensive capabilities. The report emphasizes that a fragmented defense is a vulnerable defense in the age of cyber warfare.
Future Outlook: Preparedness and Proactive Measures
Looking ahead, the 2026 Threat Assessment Report concludes with a forward-looking perspective on the future of cyber warfare and the necessary steps for sustained preparedness. It acknowledges that the threat landscape will continue to evolve, necessitating constant vigilance, innovation, and adaptation. The emphasis is on proactive measures rather than simply reacting to incidents, aiming to shape the future rather than be defined by it.
Key to future preparedness is continuous investment in research and development, particularly in areas like artificial intelligence, machine learning for threat detection, and quantum computing for secure communications. Educating the next generation of cybersecurity professionals is also paramount to ensure a skilled workforce capable of meeting future challenges. The report suggests that a whole-of-nation approach, involving government, academia, and the private sector, is the only way forward.
Strategic Investments and Workforce Development
The report advocates for a strategy that blends technological superiority with human expertise. This includes not only developing advanced defensive tools but also fostering a culture of cybersecurity awareness and resilience across all levels of society. From individual citizens to large corporations, understanding and mitigating cyber risks must become a collective priority.
- Cybersecurity Education: Implementing comprehensive educational programs from K-12 through higher education to build a robust talent pipeline.
- Public-Private Partnerships: Fostering stronger collaboration between government agencies and private industry to share expertise, resources, and threat intelligence.
- Innovation Hubs: Establishing and funding research centers dedicated to cutting-edge cybersecurity technologies and defensive strategies.
- Regulatory Foresight: Developing flexible regulatory frameworks that can adapt to rapid technological changes and emerging threats without stifling innovation.
The future of national security in the digital age hinges on the ability to anticipate, adapt, and innovate faster than adversaries. The 2026 report serves as a critical roadmap for these ongoing efforts, highlighting that preparedness is an endless journey requiring persistent commitment and strategic vision.
| Key Point | Brief Description |
|---|---|
| Escalating Threats | The report details a significant increase in sophisticated state-sponsored cyberattacks globally. |
| Key Adversaries | Identifies major state actors employing advanced tactics for espionage, sabotage, and disinformation. |
| Critical Infrastructure | Highlights vulnerabilities and impacts on U.S. essential services like energy, finance, and healthcare. |
| Defensive Posture | Outlines U.S. government strategies including zero-trust architecture and international cooperation. |
Frequently Asked Questions About the 2026 Cyber Threat Report
The report primarily focuses on analyzing the evolving landscape of state-sponsored cyberattacks against the United States. It details the methods, motivations, and increasing sophistication of these threats, particularly concerning their impact on critical infrastructure and national security.
According to the report, sectors such as energy, finance, healthcare, transportation, and government agencies are highly vulnerable. These areas are targeted due to their critical role in national functioning and the potential for widespread disruption or sensitive data acquisition.
The U.S. government is responding through enhanced defensive strategies, including deploying zero-trust architectures, investing in quantum-resistant cryptography, strengthening CISA, and fostering increased intelligence sharing with both domestic and international partners to build greater resilience.
International cooperation is crucial, as cyber threats are global. The U.S. collaborates with allies to share threat intelligence, conduct joint cyber exercises, and develop common defense protocols to collectively deter and respond to state-sponsored cyberattacks, strengthening global cyber resilience.
The report emphasizes continuous investment in AI/ML for threat detection, quantum computing research, and robust cybersecurity education. It advocates for public-private partnerships and flexible regulations to ensure proactive adaptation to evolving threats and maintain a strong defensive posture.
Conclusion
The 2026 Threat Assessment Report on State-Sponsored Attacks serves as a critical wake-up call, highlighting the pervasive and evolving nature of cyber warfare. It underscores that the digital realm is now a primary battleground for global power dynamics, with direct implications for national security, economic stability, and public trust. The U.S. government’s comprehensive approach, combining advanced technology, strategic policy, and robust international partnerships, is essential. However, sustained vigilance, continuous innovation, and a collective commitment from all sectors of society will be paramount in safeguarding the nation against the sophisticated and relentless threats of state-sponsored cyber adversaries. The report is not merely a summary of current dangers; it is a blueprint for future resilience, urging proactive engagement and unwavering dedication to cybersecurity as a fundamental pillar of national defense.